DIVD-2022-00014 - GreyNoise's Ukraine only list
| Our reference | DIVD-2022-00014 |
| Case lead | Frank Breedijk |
| Researcher(s) | |
| Recommendation | We explicitly leave it up to the network administrators to decide what to do with the observed facts |
| Status | Closed |
| Last modified | 15 Aug 2022 15:30 CEST |
Summary
GreyNoise has published a “free, public, unauthenticated, self-updating feed of all IPs that are exclusively targeting devices geographically located in Ukraine’s IP space with scans, exploits, etc.” We first became aware of it via a tweet from GreyNoise founder Andrew Morris. We feel that in these times, network administrators should be aware of these IP addresses even if they are unaware of the services of GreyNoise.
We are using the list of “unspoofed” IPs (IP addresses that have completed a full three-way handshake) located on GreyNoise Pulse. If you want to check other lists, feel free to inspect the manifest of the full API.
GreyNoise siltently stopped updating the API after 1 Aug 2022. THerefore we closed this case on 15 Aug 2022.
Overall we set 5698 notifications to owners of the IP addresses that appeared on this list. We have plotted them by the date they first hit the honeypots in the graph below.
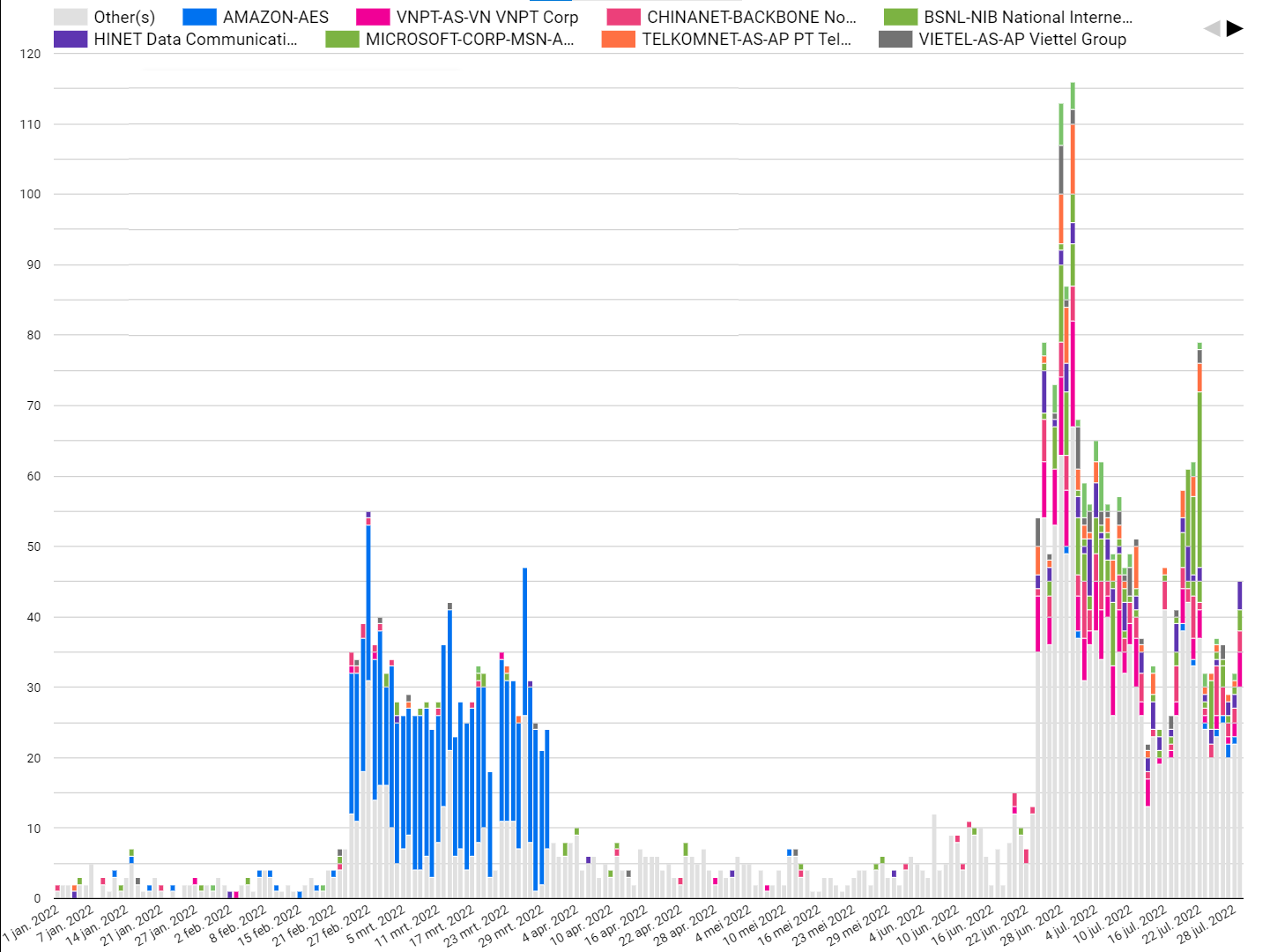
You can also interact with this graph on Google Data Studio
What you can do
We are sending out these emails for awareness only. We want you to be aware that you have one or more nodes in your network displaying this behavior. How you act on this information is entirely up to you. We cannot determine if this behavior is expected, unexpected, logical, illogical, wanted, or unwanted by you.
What we are doing
On a regular basis, we will retrieve the list from GreyNoise and send notifications to network administrators. We will only send out notifications for systems last seen on or after 1 March 2022 and only to system owners; we have not received a notification before.
Timeline
| Date | Description |
|---|---|
| 24 Feb 2022 | GreyNoise anounces their plans to publish a “free, public, unauthenticated, self-updating feed of all IPs that are exclusively targeting devices geographically located in Ukraine’s IP space with scans, exploits, etc.” |
| 04 Mar 2022 | Case opened |
| 05 Mar 2022 | First notifications sent |
| 31 Jul 2022 | Last update to the GreyNoise Ukraine only list |
| 15 Aug 2022 | Case closed |