CVE-2021-30116
Unauthenticated credential leak and business logic flaw in Kaseya VSA <= v9.5.6
| CVE | CVE-2021-30116 |
| Title | Unauthenticated credential leak and business logic flaw in Kaseya VSA <= v9.5.6 |
| Case | DIVD-2021-00011 |
| Credits |
|
| CVSS | |
| References | |
| Problem type(s) | n/a |
| Date published | |
| Last modified | 23 Oct 2023 13:12 CEST |
Description
Kaseya VSA before 9.5.7 allows credential disclosure, as exploited in the wild in July 2021. By default Kaseya VSA on premise offers a download page where the clients for the installation can be downloaded. The default URL for this page is https://x.x.x.x/dl.asp When an attacker download a client for Windows and installs it, the file KaseyaD.ini is generated (C:\Program Files (x86)\Kaseya\XXXXXXXXXX\KaseyaD.ini) which contains an Agent_Guid and AgentPassword This Agent_Guid and AgentPassword can be used to log in on dl.asp (https://x.x.x.x/dl.asp?un=840997037507813&pw=113cc622839a4077a84837485ced6b93e440bf66d44057713cb2f95e503a06d9) This request authenticates the client and returns a sessionId cookie that can be used in subsequent attacks to bypass authentication. Security issues discovered — * Unauthenticated download page leaks credentials * Credentials of agent software can be used to obtain a sessionId (cookie) that can be used for services not intended for use by agents * dl.asp accepts credentials via a GET request * Access to KaseyaD.ini gives an attacker access to sufficient information to penetrate the Kaseya installation and its clients. Impact — Via the page /dl.asp enough information can be obtained to give an attacker a sessionId that can be used to execute further (semi-authenticated) attacks against the system.
Solution(s)
Upgrade to a version after 9.5.6
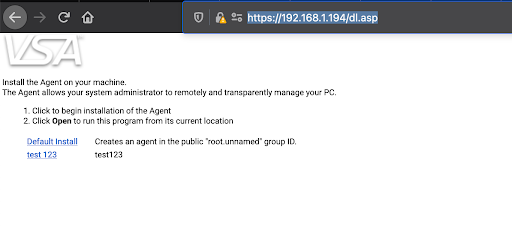
Image 1. Screenshot of dl.sap
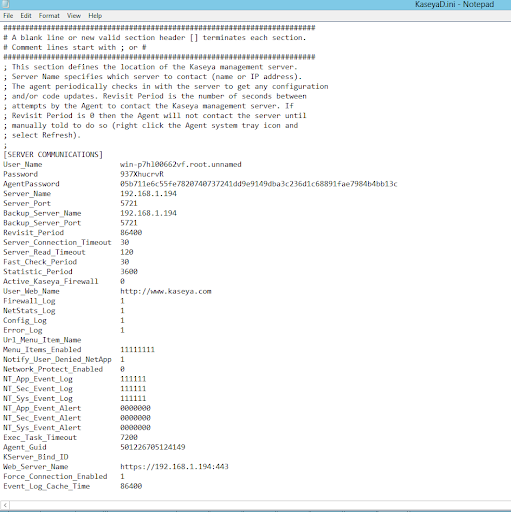
Image 2. Screenshot of KaseyaD.ini file
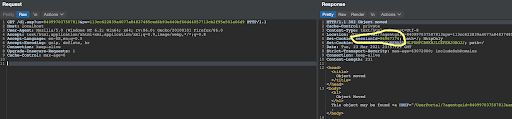
Image 3. Screenshot of obtaining a session cookie
JSON version.